The trust gap in a synthetic world: Why telecom carriers can no longer sit this one out
March 3, 2026
Leticia Latino van-Splunteren, CEO of Neptuno USA Corp; Co-founder of Albireo AI; GTWN International Board Member
US Army Brigader General Terri Borras, Senior Executive Advisor, UnCognito
As Technology leaders gather for MWC26 Barcelona, the focus is rightly on intelligent infrastructure and the systems that will shape the next decade of global connectivity. Networks are becoming more autonomous. Enterprises are integrating AI at scale. Connectivity is evolving from utility into a strategic platform that underpins economic activity, national resilience, and daily life. At the same time, trust in what we hear, see, and receive through those networks is being quietly tested.
For decades, connectivity has been synonymous with reliability. Voice calls, video meetings, and routine communications have been treated as authentic by default. That assumption shaped consumer behavior, enterprise workflows, and institutional processes across the globe. Today, it is quietly breaking down.
An employee receives a call from the CEO. The voice is familiar, the request unusual but plausible. The employee hesitates and asks for verification. A video meeting is scheduled. The faces on the screen match the leadership team the employee knows. The voices align. The context is detailed. Nothing feels out of place. The employee does what training has taught her to do. She questions. She follows process. Over the next couple of hours, a series of transfers are authorized, each one consistent with what was discussed on the call. Only later does the truth emerge. The initial voice call was synthetic. The video meeting was fabricated. The executives were never involved. By the time the deception is uncovered, millions are gone. No systems were breached. No credentials were stolen. The employee did everything right. The fraud still occurred.
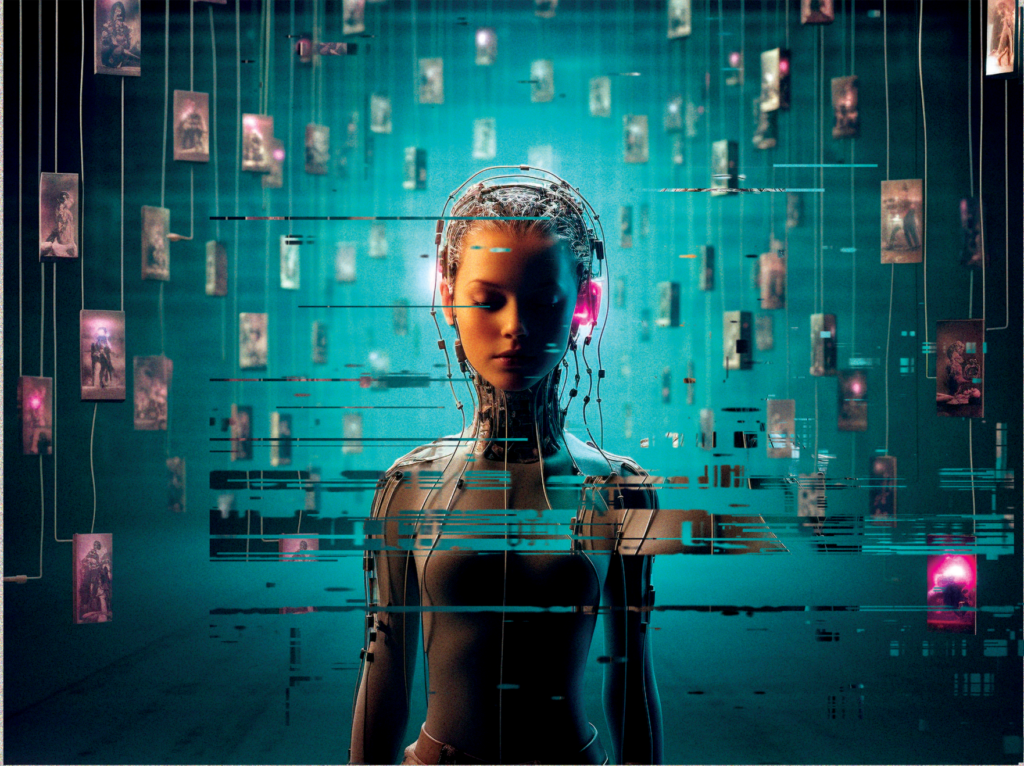
We are witnessing a broader shift created by generative AI colliding with global connectivity. Synthetic voice and deepfake content are no longer edge cases. They are reaching people and institutions in ordinary moments, through trusted networks, in ways that are difficult to detect and increasingly difficult to defend against.
A changed threat landscape
Synthetic content was once treated as a novelty or a future risk. Early deepfakes were imperfect. Detection focused on visible artifacts, unnatural speech patterns, or known signatures. The assumption was that safeguards would evolve alongside the technology, with enough time to adapt. That assumption no longer holds.
Generative AI has advanced rapidly over the past two years. Synthetic voices now replicate emotion, accent, cadence, and conversational flow with unsettling accuracy. In some cases, only a few seconds of audio are required to convincingly clone a voice. The barrier to entry has collapsed.
These attacks are not about scale alone. They are about precision. They succeed by exploiting stress, authority, and familiarity rather than technical vulnerabilities. Precision reduces noise. Credibility increases success rates. Speed limits opportunities for verification. The result is a form of deception that is harder to detect, faster to execute, and more corrosive to trust.
Crucially, these attacks travel across the same networks people depend upon for their most important communications: calls from family members, instructions from supervisors, confirmations from institutions, and requests that appear routine until it is too late.1
Why telecom sits at the trust boundary
Anyone who has attended Mobile World Congress over the past decades will remember when the show floor was dominated by physical network equipment, switches, base stations and antennas built with a singular purpose: to enable communication at scale. The industry set out to build the global data highway, and by any measure, it succeeded.
Voice became ubiquitous, connectivity dependable, and trust an implicit byproduct of reliability. When a consumer hears a voice on a phone line, authenticity is assumed by default.2 What has changed is not the infrastructure, but what now travels across it. The same networks engineered for speed, clarity, and scale are increasingly carrying synthetic voices and manipulated media that can convincingly impersonate real people. No systems are breached.
Nothing “breaks.” Yet the outcome can be deception and loss of confidence. This is the inflection point for telecom. Having mastered connectivity, the industry now carries a broader responsibility, not just to move information, but to help safeguard the authenticity of what moves through its networks. Carriers are no longer only builders of the data highway; as policy makers struggle to find ways to protect consumers, Telecom Operators are organically being placed at the boundary between human trust and machine-generated signals. Responsibility follows position within the ecosystem. As networks gain intelligence, they also inherit consequence. Once AI begins to automate planning, optimization, and decision-making at the network level, questions of trust can no longer be treated as externalities. They become part of the system’s core behavior.
Consumer protection as an infrastructure responsibility
Consumer protection in this environment cannot be treated as a feature, a premium service or an afterthought. Synthetic voice fraud does more than cause financial loss. It erodes confidence. When people begin to doubt what they hear, hesitation replaces participation. Over time, that hesitation spreads, affecting adoption, inclusion, and trust in digital systems more broadly.
Telecom carriers already intervene to limit spam, robocalls, and network abuse. Trust has always been part of the mandate. What has changed is the nature of the threat. Synthetic attacks increasingly target individuals, families, and employees at moments of stress or urgency.
As consumers lose confidence in voice communication, institutions may shift toward more complex verification processes, adding friction and cost. Enterprises may hesitate to rely on voice-based workflows. Ignoring this challenge risks reputational damage, regulatory pressure, and long-term trust decay.3 Addressing it, by contrast, positions Carriers as stewards of digital integrity at a time when confidence in digital systems is under active strain.
What effective protection looks like
Protecting against synthetic content does not require telecom carriers to moderate speech or judge intent. It requires the ability to distinguish authentic human signals from machine-generated ones at scale.
Across the industry, more effective approaches are beginning to share common characteristics. They operate in real time or near real time. They scale across global traffic. They preserve privacy. They remain resilient as generative models evolve. Methods that rely solely on known signatures or static training data struggle to keep pace with rapidly changing tools. As generative models update, detection systems trained on yesterday’s patterns fall behind.
More durable approaches focus on the physical characteristics of sound and signal behavior that are difficult to replicate convincingly at scale. These characteristics persist even as models improve, offering a more stable foundation for assessment. Across current industry efforts, one lesson is becoming clear. Scale and speed matter as much as accuracy. Detection that works only in controlled environments or post-event analysis does little to protect people in real time.
When integrated thoughtfully, these capabilities do not interrupt communication. They restore confidence in it. For carriers, this offers a path to strengthen consumer protection and enterprise trust without adding friction or compromising privacy.
A leadership moment at MWC’26
As Intelligence Infrastructure becomes the backbone of economies and societies, trust can no longer remain implicit. It must be engineered, maintained, and defended.4
This is a call for recognition, not perfection. Leadership at this stage does not require perfect answers. It requires acknowledgment, collaboration, and early action. It requires telecom and technology leaders to treat trust as a system property rather than an assumed condition.
Connectivity has always been about bringing people closer. As intelligence is increasingly layered into networks and the services that depend on them, protecting authenticity becomes central to sustaining trust at scale. Are we ready, industry, operators, and leaders alike, to treat trust as a system we design, not an assumption we inherit?
- Synthetic voice fraud and AI-enabled impersonation. U.S. Federal Trade Commission, Consumer Alert: Scammers Use AI to Clone Voices; Europol, Facing Reality? Law Enforcement and the Challenge of Deepfakes (2023). ↩︎
- Voice networks as trusted communication channels. GSMA, Understanding Fraud and Security in Telecom Networks; ETSI, Trust and Identity in Telecommunications Systems. ↩︎
- Regulatory scrutiny and consumer protection. U.S. Federal Communications Commission, Consumer Protection and Robocall Mitigation Reports; European Commission, AI Act: Implications for Impersonation and Fraud. ↩︎
- Trust as an infrastructure property. OECD, Building Trust in the Digital Economy; World Economic Forum, Global Risks Report: Digital Trust and Infrastructure Resilience. ↩︎
Leticia Latino van-Splunteren is a global telecommunications and technology executive with more than 25 years of experience across telecom infrastructure, software, and AI-driven platforms. She is the CEO of Neptuno USA Corp and co-founder of Albireo AI, an AI-native company applying digital twins, advanced analytics, and conversational AI to telecom infrastructure.
She has held senior advisory roles shaping U.S. broadband and workforce policy, including Committee leadership positions with the FCC, WIA and NATE. Leticia serves on multiple for-profit and nonprofit boards including the US National Wireless Safety Alliance and the Global Telecom Women’s Network.
She also currently advises New Space companies through the European Innovation Council Scaling Club. She is a recognized author, public speaker, podcast host and industry mentor.
Terri Borras is a senior executive advisor with more than three decades of experience across national security, emerging technology, and enterprise transformation. Her work focuses on trust, risk, and decision-making in complex, technology-enabled environments.
She currently works with UnCognito, advising on product strategy, innovation, and emerging technology risk related to synthetic content and trust in global communications. Terri also advises public- and private-sector leaders and is a published author and speaker on technology risk and leadership in the digital era.






